The arrest of a man attempting to scale the perimeter of the Israeli embassy in London has stripped away the veneer of competence surrounding current border enforcement strategies. It is not just a story of a security breach. It is a story of a system that keeps records of its failures but lacks the mechanics to act upon them. When the suspect appeared in court, the revelation that he had entered the United Kingdom via small boat crossings on two separate occasions turned a localized police incident into a national security indictment.
Security services often speak of "known quantities." In this instance, the suspect was known to the Home Office, known to border officials, and known to the system that tracks illegal arrivals. Yet, he was still able to approach one of the most sensitive diplomatic sites in the capital. The failure here is not with the guards on the gate, who did their jobs. The failure is the administrative black hole that exists between an arrival on a beach and a criminal act in the city.
The Repeating Pattern of Small Boat Arrivals
The court proceedings highlighted a specific, uncomfortable reality about the current immigration crisis. The suspect did not just slip through the cracks once. He arrived via a small boat, was processed, and then somehow found himself in a position to attempt a second crossing or remain in a state of legal limbo that allowed for a second entry record. This creates a circular problem for law enforcement.
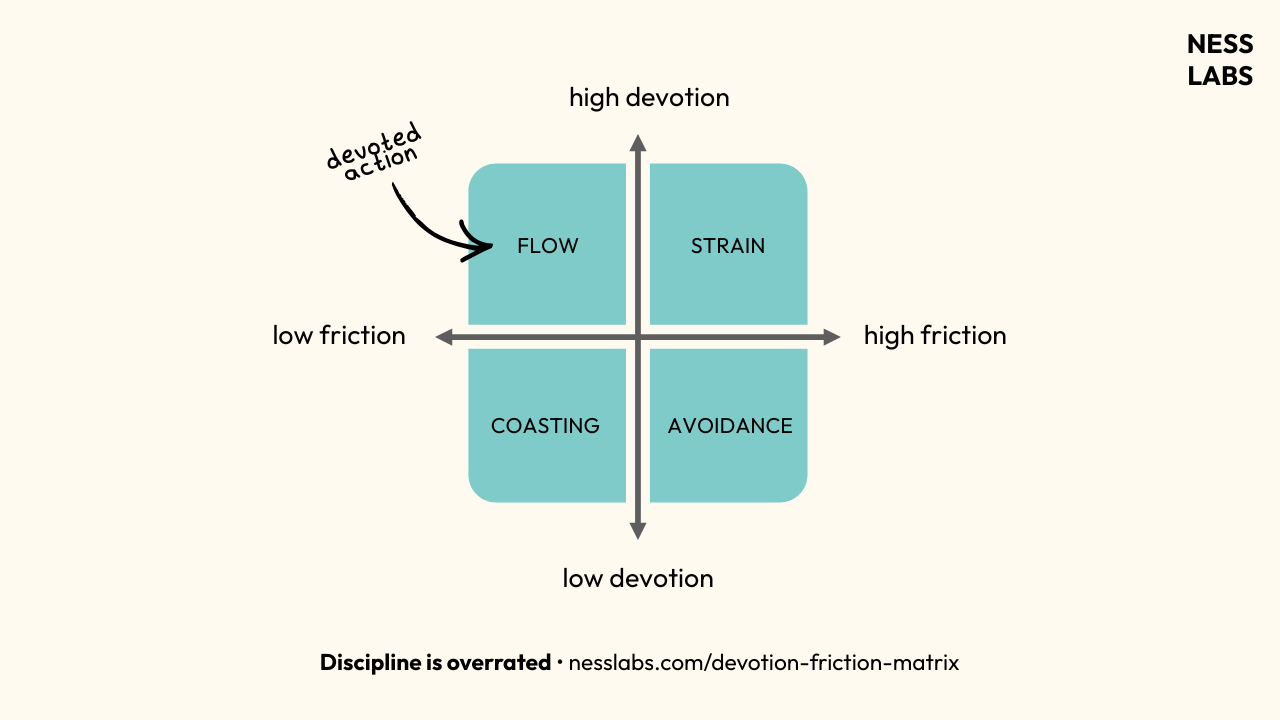
When a person enters the country outside of official channels, the state begins a data file. They take biometrics, they record a name, and they assign a case number. However, the sheer volume of these files has created a backlog where "processing" has become a substitute for "resolution." We are seeing a high-frequency loop where individuals are recorded entering the country, but the subsequent monitoring is practically non-existent.
This specific case involving the Israeli embassy highlights that the risk is not just about numbers or economics. It is about the inability to vet the intentions of those arriving. If the state cannot prevent a two-time arrival from targeting a high-profile embassy, it suggests that the current database of arrivals is a library of names rather than a tool for prevention.
The Intelligence Gap in Diplomatic Protection
Diplomatic missions are supposed to be the most secure zones in any major city. The Israeli embassy, in particular, operates under a state of permanent high alert due to the geopolitical climate. Security at these sites relies on two things: physical barriers and preemptive intelligence.
The physical barriers worked. The suspect was apprehended before he could cause harm or gain entry to the interior. But the intelligence side of the equation failed long before he reached the fence. The fact that an individual with a history of irregular entry—a clear red flag for potential instability or lack of vetting—could move freely toward such a target indicates a total breakdown in communication between border agencies and local counter-terrorism units.
The Problem of Distributed Data
One of the biggest hurdles in modern British security is that data is siloed. The Home Office holds the records for small boat arrivals. The Metropolitan Police handle local security and diplomatic protection. While they technically share databases, the "triggers" for an alert are often too high.
- Arrival Data: Often lacks deep background or verified identity.
- Behavioral Monitoring: Usually only kicks in after a crime is committed.
- Preventative Action: Hampered by legal constraints and a lack of physical space in detention centers.
We are operating in an environment where the authorities are recording the "who" and the "when" but have no capacity to manage the "what happens next." This man was a data point on a spreadsheet until he became a body on a fence.
Why Deportation is a Paper Tiger
The court heard that the suspect had arrived twice. To the average observer, this raises an obvious question: why was he here to make a second trip? The answer lies in the collapse of the deportation mechanism.
A deportation order is often little more than a piece of paper. For many arrivals, there is no direct return agreement with their country of origin. This results in a "limbo population"—people who the state knows have no right to be here, but who cannot be moved. They are released into temporary accommodation or, in many cases, simply disappear from the official radar.
When the system fails to remove someone after their first irregular entry, it signals that the border is effectively a revolving door. The suspect in this case knew the process. He had navigated it twice. He understood that being caught at the border did not lead to an immediate exit, but rather to a path into the interior of the country. This lack of consequence emboldens individuals who may have more than just economic survival on their minds.
The High Cost of Selective Security
We spend millions on the "ring of steel" around London’s diplomatic quarter. We have armed officers, facial recognition, and reinforced bollards. But all that hardware is a last resort. True security is found at the point of entry.
If the government continues to focus on the optics of border patrols without fixing the back-end reality of what happens to those who are intercepted, these incidents will increase. The Israeli embassy attempt is a warning shot. It demonstrates that the current chaos at the English Channel has a direct downstream effect on the safety of our streets and the integrity of our international obligations.
The Resource Drain
Every time an individual with this kind of background commits a high-profile act, it triggers a massive deployment of specialized resources.
- Specialist Firearms Command (MO19) is put on high alert.
- Counter Terrorism Command (SO15) must open an investigation.
- Diplomatic Protection (PaDP) has to review all standing orders.
These are finite resources being spent to manage a crisis that should have been resolved at the coastline. The financial and operational drain of monitoring a growing population of unvetted, irregular arrivals is reaching a breaking point.
Redefining the Threat Assessment
For years, the political debate around small boats has centered on "fairness" and "compassion." This court case forces a shift toward "risk." It is no longer possible to view irregular arrivals solely through a humanitarian lens when the security apparatus is flagging individuals who pose a direct threat to sensitive sites.
The threat assessment needs to be updated to account for the "rebound effect"—individuals who are intercepted, released, and then go on to engage in activities that threaten public order or national security. The current system assumes that once someone is in the "processing" phase, they are no longer a risk. This is a dangerous fallacy.
The man at the embassy fence wasn't a ghost; he was a registered entity in the state's own system. The state had two chances to identify a potential issue and twice it opted for the path of least resistance.
The False Security of the "System"
The public is often told that the border is "under control" because the numbers of interceptions are high. This is a fundamental misunderstanding of security. Interception without enforcement is just a census of the incoming.
When a suspect appears in court and his history of illegal entry is read out like a routine biography, it reveals how normalized the failure has become. The judicial system is now the first place where the full picture of an individual’s history is actually scrutinized, long after they have had the opportunity to scout targets or plan an intrusion.
The security at the Israeli embassy held this time. But the next person to scale a fence might not be an amateur, and they will likely have the same history of "known" entries that the state failed to act upon. We are currently relying on the alertness of individual officers to compensate for a systemic collapse in border integrity.
A border that records everyone but stops no one is not a border; it is a ledger of future liabilities.