The issuance of a high-level security alert based on an unverified tip represents a fundamental breakdown in the intelligence-to-action pipeline. When the FBI broadcasts a warning regarding potential Iranian retaliation—only for the White House to subsequently clarify the data’s lack of corroboration—the primary casualty is the credibility of the national threat signaling system. This discrepancy reveals a friction between two competing institutional imperatives: the "Duty to Warn" versus the "Requirement for Validation."
The current friction point centers on reports of Iranian-backed threats targeting U.S. infrastructure or officials. To analyze the strategic implications of this specific intelligence cycle, one must look past the headlines and examine the structural mechanics of how unverified data enters the public record and the cascading costs of "false positive" alerts in geopolitical signaling.
The Tri-Node Intelligence Filter
National security alerts typically pass through a three-stage filtration process before reaching public or law enforcement distribution. The failure of any single node results in the public dissonance currently observed between the Department of Justice (DOJ) and the Executive Branch.
- Sourcing and Collection (The Raw Signal): At this stage, data is categorized by reliability (e.g., a human source with a proven track record vs. an anonymous tip). The current Iranian retaliation narrative appears stuck at this entry point.
- Analysis and Corroboration (The Validation Layer): Analysts look for "all-source" confirmation. If a human source claims a plot is active, signals intelligence (SIGINT) or imagery intelligence (IMINT) should, in theory, show corresponding movement. The White House’s insistence that the tip is "unverified" indicates that this second layer failed to find supporting evidence.
- Dissemination Strategy (The Threshold Decision): This is a risk-mitigation calculation. If the cost of an undetected attack is $C$ and the probability of the threat being real is $P$, the agency must decide if $P \times C$ outweighs the reputational and operational cost of a false alarm.
The FBI’s decision to issue an alert suggests they have lowered the $P$ threshold for Iranian-related threats, likely due to the heightened geopolitical stakes in the Middle East. However, when the White House publicly distances itself from the verification of that data, it creates a "Signaling Gap" that adversaries can exploit to measure U.S. internal coordination.
The Asymmetry of Retaliation Logic
Iranian strategic doctrine does not prioritize immediate, impulsive strikes. Instead, it operates on a "Calculated Proportionality" framework. Understanding this framework explains why "unverified tips" are often more reflective of noise than actual imminent kinetic action.
The Strategic Patience Variable
Tehran’s retaliatory cycles—dating back to the 2020 response to the Qasem Soleimani strike—demonstrate a preference for "Theater Signaling." They often seek targets that provide high symbolic value with manageable escalatory risks. An unverified tip regarding a domestic U.S. strike often fails the logic of Iranian strategic interest, as a successful domestic attack would likely trigger a full-scale conventional response that the Iranian regime is currently ill-equipped to survive.
The Cyber-Kinetic Substitution
The "cost function" of a physical assassination or bombing on U.S. soil is prohibitively high for a state actor. In contrast, cyber-ops or influence operations offer plausible deniability. Intelligence agencies frequently miscategorize "chatter" regarding cyber-targeting as physical threat indicators, leading to the type of public-facing alerts that the White House must later walk back to prevent domestic panic or unnecessary diplomatic escalation.
Structural Hazards of High-Frequency Alerting
The issuance of unverified warnings creates three distinct operational hazards that degrade long-term national security.
- Desensitization (The Cry Wolf Effect): Law enforcement agencies at the state and local levels possess finite resources. When federal alerts are issued and subsequently caveated as "unverified," the "Signal-to-Noise Ratio" decreases. Over time, local responders may deprioritize federal bulletins, leading to a delayed response when a verified, high-probability threat finally emerges.
- The Resource Drain Paradox: Every FBI alert triggers a mandatory set of protocols across thousands of police departments. The cumulative man-hours spent investigating "unverified" leads constitute a massive hidden tax on the domestic security apparatus. This is a form of "Economic Attrition" where the adversary achieves a win simply by causing the U.S. to misallocate billions in security spending on ghost threats.
- Adversarial Probing: Foreign intelligence services (including Iran’s MOIS) monitor the U.S. response to these leaks. By planting "unverified" information through third-party channels, an adversary can map the FBI’s internal reporting thresholds and identify the specific bureaucratic friction points between the DOJ and the White House.
The Taxonomy of "Unverified" Information
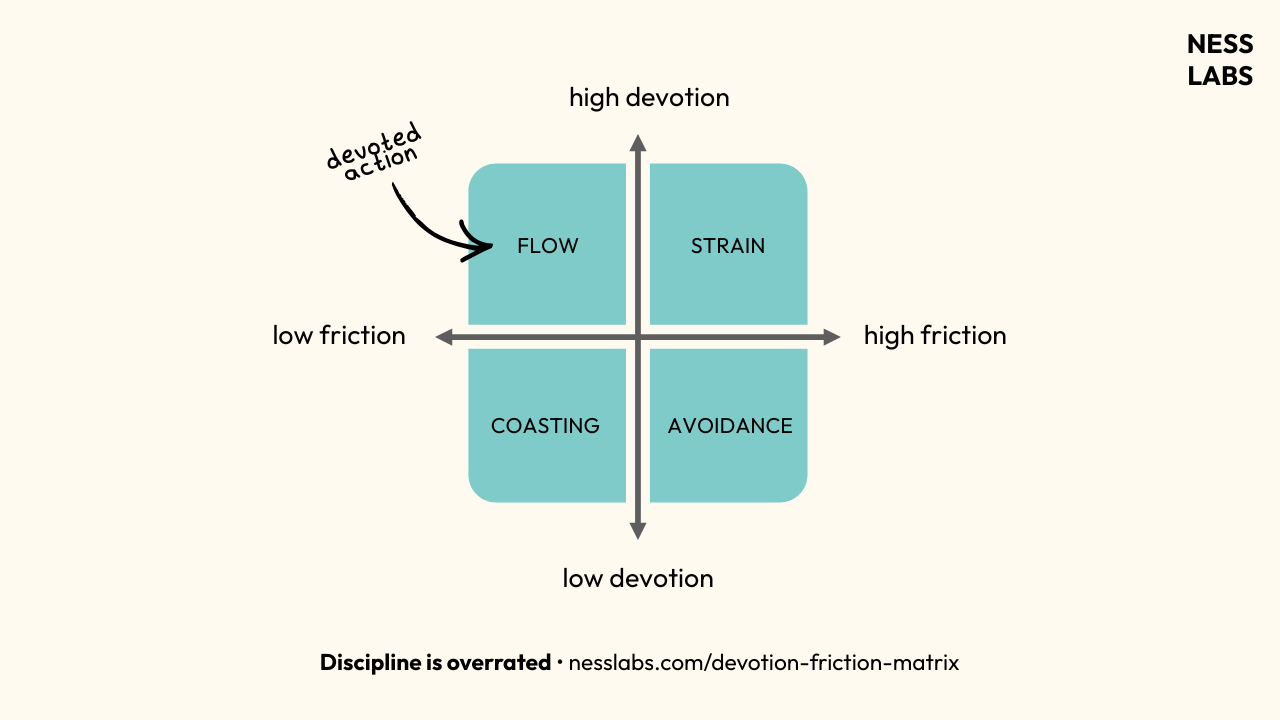
In the realm of strategic intelligence, "unverified" is not a synonym for "false." It represents a specific state of data maturity. We can categorize these tips into four distinct quadrants based on their origin and utility.
- Organic Noise: Random data points from the public or low-level informants that lack context.
- Deliberate Disinformation: False leads planted by adversaries to distract or test response times.
- Fragmentary Intelligence: Real pieces of a larger puzzle that cannot yet be connected to a specific actor or timeline.
- Preemptive Leaks: Information shared by an agency specifically to "disrupt the environment" and let the adversary know they are being watched, regardless of the data's accuracy.
The White House's clarification suggests that the recent FBI alert may have fallen into Category 4—a strategic leak intended to deter Iran by signaling awareness. However, the lack of inter-agency alignment on the "unverified" status suggests a tactical error in communication rather than a unified deterrent strategy.
Intelligence Calibration and the Path to Verification
The discrepancy between the FBI and the White House highlights a need for a "Standardized Confidence Interval" in public reporting. Currently, the U.S. government lacks a public-facing metric to communicate the reliability of a threat.
- Low Confidence: Information is unconfirmed, sourced from a single point, or lacks logical consistency with known adversary behavior.
- Moderate Confidence: Information is credible but lacks specific "Time, Place, and Manner" details.
- High Confidence: Information is corroborated by multiple independent streams and shows active preparation by the adversary.
The FBI alert skipped these distinctions, presenting a "Low Confidence" tip with the urgency of a "High Confidence" threat. This creates an "Expectation Gap." When the public expects an imminent event that never materializes, the government’s ability to manage future crises is compromised.
The pivot from raw data to actionable intelligence requires a rigorous "Red Teaming" of every tip. If the FBI receives a report of Iranian retaliation, the first question should not be "How do we warn the public?" but rather "Does this tip serve the adversary’s goal of psychological warfare?" By failing to ask the latter, the bureau inadvertently becomes a megaphone for Iranian influence operations.
Strategic Realignment Requirements
To correct this intelligence discontinuity, the security apparatus must adopt a "Risk-Averse Reporting" model. This does not mean withholding information, but rather contextualizing it within the broader geopolitical landscape.
The immediate tactical move for domestic agencies is to decouple "Law Enforcement Awareness" from "Public Notification." The FBI can alert local precincts to be vigilant without triggering a national news cycle that requires a White House correction. This containment strategy prevents the weaponization of unverified tips by foreign actors and preserves the "Signaling Power" of the Executive Branch for when a verified, existential threat actually arrives.
The focus must shift toward a "Verification-First" culture. In a high-tension environment involving state actors like Iran, the cost of a public retraction is often higher than the cost of a delayed, but accurate, warning. The objective is to maintain a posture of "Quiet Readiness" rather than "Loud Uncertainty." Future alerts must be gated by a mandatory inter-agency "Correlation Check" to ensure that the DOJ and the White House are reading from the same analytical ledger before the first headline is ever written.